What is the dark web and how does it vary from the internet most of us use everyday? Which darknet should I use for my investigation? And how can I access it safely?
The dark web is a small part of the internet reachable only with special software (e.g., Tor) where .onion sites aren’t indexed by search engines. Access isn’t illegal in most jurisdictions, but many activities there are. Investigators should use non-attributable, isolated browsing with full auditing to reduce legal, security, and privacy risk.
Here's a quick overview of some of the dark web topics we'll cover.
Surface vs. deep vs. dark web (at-a-glance):
- Surface web: Public pages indexed by search engines; open access
- Deep web: Content behind logins/subscriptions (e.g., databases, SaaS); not indexed
- Dark web: Hidden services (.onion, I2P, Freenet) accessible only via specialized clients
How to access the dark web safely (for investigators):
- Use an isolated, anonymous, and secure browser like Silo to prevent host exposure
- Enforce non-attribution (managed identity, location, language, time)
- Log and audit all actions for legal defensibility
- Apply read-only controls and malware detonation barriers
- Follow policy and legal guidance; avoid engagement on illicit forums
What’s on the dark web?
Perhaps best known for its association with illicit activities, the dark web has become infamous for its role in the illegal drug trade. But there are less nefarious reasons to access the encrypted dark web. In many countries, the dark web allows demonstrators to subvert authoritarian regimes and provides a free and open internet model that can evade censorship and provide privacy.
Dark web sites are similar in content and style to the surface web, or the internet most people are familiar with, but the traffic is routed and shared differently, making it more difficult to shut down or find the original sources of content.
For investigators, it can hold crucial information that would otherwise be inaccessible. To acquire these datasets, it is important to understand each area of the web, the different clients available to use them and what precautions should be taken before diving in.
Is the dark web illegal?
The dark web isn't inherently illegal. It's what you do on the dark web that leads you to the blurred lines of legality.
The dark web is infamous for illicit underground dark web marketplaces selling contraband across international borders. The Silk Road rose to notoriety in 2011 after an article was featured on the then-popular site Gawker. The Silk Road was eventually shuttered by law enforcement agents in 2013. But since the bust, several more dark web markets have appeared in its wake, each seeming more competent then the last. Well-known dark web marketplaces for illegal drug sales and other items include Alpha Bay, Agora, and countless others.
The digitized version of the black market means the contraband being offered can go further in larger quantities than any physical predecessor. It also sells more than the illicit substances it's often known for, contraband can include stolen data, illegal firearms and exploitation material. These dark web commerce sites are often powered by cryptocurrency, so the users can shroud their purchases in purported anonymity.
So with all this illegal activity taking place on to the dark web, is it really okay to log on? While the nature of the dark web has led to abuses and exploitations by bad actors, this underside of the internet is not illicit by nature. The dark web can be a beacon of free speech in authoritarian countries.
Free speech on the dark web
The dark web’s role as an anonymous and reliable source of information to dissidents in foreign countries, alongside privacy enthusiasts, is important and legitimate. Many reputable websites have mirrored dark web versions of their website, including news organizations like the BBC, The New York Times and ProPublica.
Just because you can’t get there by popular search engine doesn’t automatically make it nefarious. But it’s important to know the legal, security, and privacy implications that come with before attempting to logon to the dark web for research or any other reason.
It may not be illegal to access the dark web, but doing so comes with considerable risks. The dark web is a place where stumbling into the wrong place (including illegal places) is easy to do. Be sure to read the risks and implications section to learn more.
What is the surface web?
The internet most of us use daily—and probably assumed until now is the entirety of the internet—is actually what’s known as the open web or surface web. It is the format of the web we’re all used to, composed of open pages easily accessed by traditional search engines on any browser. Despite being where so many users default to, the surface web only accounts for a small portion of the entire internet.
What is the deep web?
The deep web is the next layer of internet information. These are sites that require login or subscription services to access, such as academic journals, court record databases, or even services like Netflix. The deep web has some barriers to accessibility while being adjacent to the surface web and is typically accessed via the same browsers.
Surface web vs. deep web vs. dark web
Understanding how the surface web, deep web, and dark web differ is essential for investigators conducting online research safely and effectively.
While the surface web is open and easily searchable, the deep web contains valuable but restricted information behind logins or paywalls. The dark web, by contrast, exists on encrypted networks that hide user identity and site locations. For investigators, the dark web can hold critical intelligence—but safe, non-attributable access through an isolated browser is essential to avoid exposure or legal risk.
Here is some key information at-a-glance about the surface web, deep web, and dark web.
Dark web networks and possible risks
To access the dark web, a special software or client is needed. Each version of the dark web provides its own dataset, encryption services and risks from attempting to access it.
The Tor browser
The most commonly used darknet service is the Tor browser. It stands for The Onion Router, developed by the U.S. Naval Research Laboratory in 2002. It was created to provide layers of encryption (hence the reference to onions) in order to anonymize communication between intelligence professionals. Tor operates almost like a traditional web browser; you can download it to your machine and use it to access different sites.
By diverting traffic through multiple nodes on its way to the client, the originator of files and sites can be hidden, making them more difficult to trace. The multi-layered encryption gives anonymity to its users and service providers alike. Many sites are given a random URL that ends in .onion. Anyone can download the Tor browser onto their machine, but like any other browser, there are still ways to track activity and hacking risks.
In the Tor browser, the biggest weakness is the point information travels between the exit node and the destination site. This unencrypted area presents a vulnerability to users.
ZeroNet
Lesser known darknets include ZeroNet, a peer-to-peer-based web hosting model developed in 2015 that doesn’t use IP addresses or domains for websites. Sites are not hosted via a typical service and can only be accessed by public key. It makes sites free to create and share and almost impossible to shut down.
To access ZeroNet, you can use a regular browser with the application running in the background. Information from it can also be downloaded and made available offline. The content is made available via BitTorrent, which shares bits of information across many peers, each one hosting a piece of the information needed. By distributing the information through many hosts, it makes it nearly impossible to track down or scrub all of the pieces of content from the web. Each peer can then reshare and distribute themselves once they have downloaded it.
Unlike Tor, ZeroNet is not anonymous.
I2P, Invisible Internet Project
Another network is I2P, or the “Invisible Internet Project,” released in 2003. Unlike the previous two sources for websites and file sharing, I2P focuses mostly heavily on encrypting communication between users. Unlike Tor, it encrypts via a peer-to-peer model instead of a single thread.
Access to I2P uses a browser and an application in the background. It provides untraceable communication by establishing one-way tunnels through peers. Each client becomes a node in the tunnel and tunnels then expire after 10 minutes. The system is referred to as “garlic routing.” The one-way messages are encrypted for recipients, as well as their delivery instructions.
Freenet
Freenet is another peer-to-peer network for sharing decentralized data created in 2000. It is used in two forms: the “opennet” allows connection to any user, while the “darknet” connects only to friends. The ability to access only known contacts provides a higher degree of trust than other software.
Access is created through a backend web application and requires a key to access. While it was originally used by dissidents to circumvent censorship laws, it is now popularly used by cyber criminals to offload stolen and malicious content.
The traffic is routed via the closest nodes in the open net to create efficient routing. In the darknet, routes are set up manually and only trusted parties know your node’s IP address. The inconvenience of the darknet infrastructure is outweighed by the security it provides. In this system, the information stays available after the publisher has disconnected.
Use cases for dark web networks
Here are the key use cases, pros, and cons between the most common dark web services (Tor, ZeroNet, I2P, and Freenet).
| Dark web service | Common use cases | Pros | Cons |
| Tor (The Onion Router) | Anonymous browsing, hosting hidden services, communicating securely under surveillance |
|
|
| ZeroNet | Peer-to-peer website hosting and file sharing |
|
|
| I2P (Invisible Internet Project) | Secure peer-to-peer communication and messaging |
|
|
| Freenet | Decentralized file storage and data sharing |
|
|
Should you access the dark web for your investigation?
Each of these darknet services can benefit investigators of law enforcement agencies, intelligence practitioners, financial services analysts and other researchers. The dark web can be a resource to help evaluate leads, corroborate or disprove information and track data leaks. The dark web can also provide the context of how criminal marketplaces are operating and what tactics are being used to commit hacks or to track stolen data.
Many hackers discuss trade secrets in dark web forums. This information can help mitigate cyberthreats before they are committed or be used to recover leaked data from a breach. They may also post leaked passwords and accounts or sales of hacked devices. Financial crimes are often the subject of posts too. Stolen online bank account access or credit cards may be traced on the dark web.
When tips come in, following them in all places they lead may necessitate dark web access and help gain information on how bad actors operate.
Implications and risks of dark web research
Despite the benefits, many may have reasonable doubts and concerns about accessing the dark web. While accessing it is not illegal per se, it is important to take steps to mitigate any risks or potential legal threats, especially when entering areas of the dark web where illegal activity is being conducted. Dark web research requires careful policies, auditing abilities and security measures before logging on.
→ Here are a few tips to keep in mind on what not to do on the dark web.
First, develop processes and procedures for your company and any employees who may be utilizing the dark web for their research. Be sure to consult your company’s legal counsel in this step, as they will have the best guidance for your circumstances and organization.
Since dark web marketplaces or forums are often monitored by law enforcement, it can be difficult to distinguish between criminal actors and good faith investigators. Avoid implications or attributions by having a plan. Be sure to document your plan of operation before gathering information or accessing a criminal forum. Maintain a complete record of activities while on the dark web and have a policy in place for “rules of engagement” when on sites where criminal activity may occur.
For more resources on the legality of dark web access, consult "Legal Considerations when Gathering Online Cyber Threat Intelligence and Purchasing Data from Illicit Sources" by the United States Department of Justice.
Other risks include the security of investigators and their machines. While the dark web’s purpose is to provide some anonymity, there are still risks of malicious content or attribution when accessing. The safest way to gain access is by using a secure cyber-service product.
How do you safely access the dark web?
Every investigator, analyst, and security professional knows the importance of being able to access the dark web safely. But doing so without burning your cover, exposing your organization, or inadvertently stumbling into legal trouble is where operational tradecraft matters. When it comes to having first-hand access, there are two paths: the traditional do-it-yourself method and the purpose-built alternative. Neither is wrong. But they're not equal.
Traditional, Do-it-Yourself (DIY) Approach: Build and Maintain Your Own Resources
Investigators who've tried to stand up dark web access the manual way know how "I'll just download Tor" can turn into a long exercise in operational security configuration that usually starts with petitioning their IT security team for a policy exception. But for this discussion, we’ll assume all of that has been accomplished. Done properly, the following do-it-yourself approach to dark web works. But, if this process is not implemented properly, any number of missteps could lead to incredibly damaging exposure.
Step 1: Obtain a dedicated device
Acquire a burner laptop, which is a machine purchased with cash, never logged into any corporate or personal accounts, and used exclusively for investigative work. The alternative to this is building an entire dirty network, which will be a convoluted series of VPNs that resolve to an endpoint that has no connection to the corporate or personal identity of the user. Both have financial and security oversight complications.
Step 2: Harden the operating system
Install a privacy-focused operating system such as Tails (which routes all traffic through Tor by default and leaves no trace on the host machine) or Whonix. Standard Windows or macOS configurations carry too much ambient data and behavioral telemetry to be appropriate for sensitive investigations.
Step 3: Configure network-level anonymization
Download and configure the Tor Browser from the official Tor Project site. It’s importabt to verify the cryptographic signature before installing because malicious Tor lookalikes exist and have been used to de-anonymize researchers (which would defeat the purpose of downloading Tor Browser). At this stage, it’s also wise to consider layering a reputable virtual private network (VPN) before the Tor entry node for additional obfuscation, though this introduces its own trust dependencies.
Step 4: Establish a clean network path
Never access the dark web from your home network, corporate network, or any network tied to your real identity. Use a public Wi-Fi location that isn't routinely associated with your movements, or consider a dedicated mobile hotspot paid for anonymously. While this will again increase costs or reduce convenience, nothing is more costly than being compromised.
Step 5: Create and maintain investigative personas
Develop cover identities appropriate to the forums or marketplaces being accessed. This means consistent usernames, backstories, posting histories, and behavioral patterns. Persona management is an ongoing tradecraft discipline, not a one-time setup.
Step 6: Establish a virtual environment within your laptop and implement read-only discipline
Never download files directly to the investigative device. Malware-laden files are common on Dark Web forums, and a single careless click can compromise the entire operational stack. Any files that must be collected should be handled in an isolated virtual machine environment, which means downloading VMWare, Microsoft Hyper-V, or any number of alternatives to establish the required virtual environment(s).
Step 7: Establish audit and documentation procedures
Before accessing any dark web resource for investigative purposes, document the operational plan, legal authority, and rules of engagement. Maintain timestamped logs of all activity. This isn't bureaucratic box-checking; it's the chain of custody that determines whether findings hold up later.
Step 8: Consult legal counsel
Organizations should have policies governing dark web access before (not after) anyone logs on. The U.S. Department of Justice's guidance on legal considerations for online cyber threat intelligence is a useful starting point, but organizational legal counsel should review any investigative program before it launches.
Silo Approach: Integrated, Managed, and Operational in Minutes
Silo Workspace was built for investigators who need dark web access that's secure by design rather than secure by assembly. The difference is significant, both in setup time and in the reliability of the protections themselves.
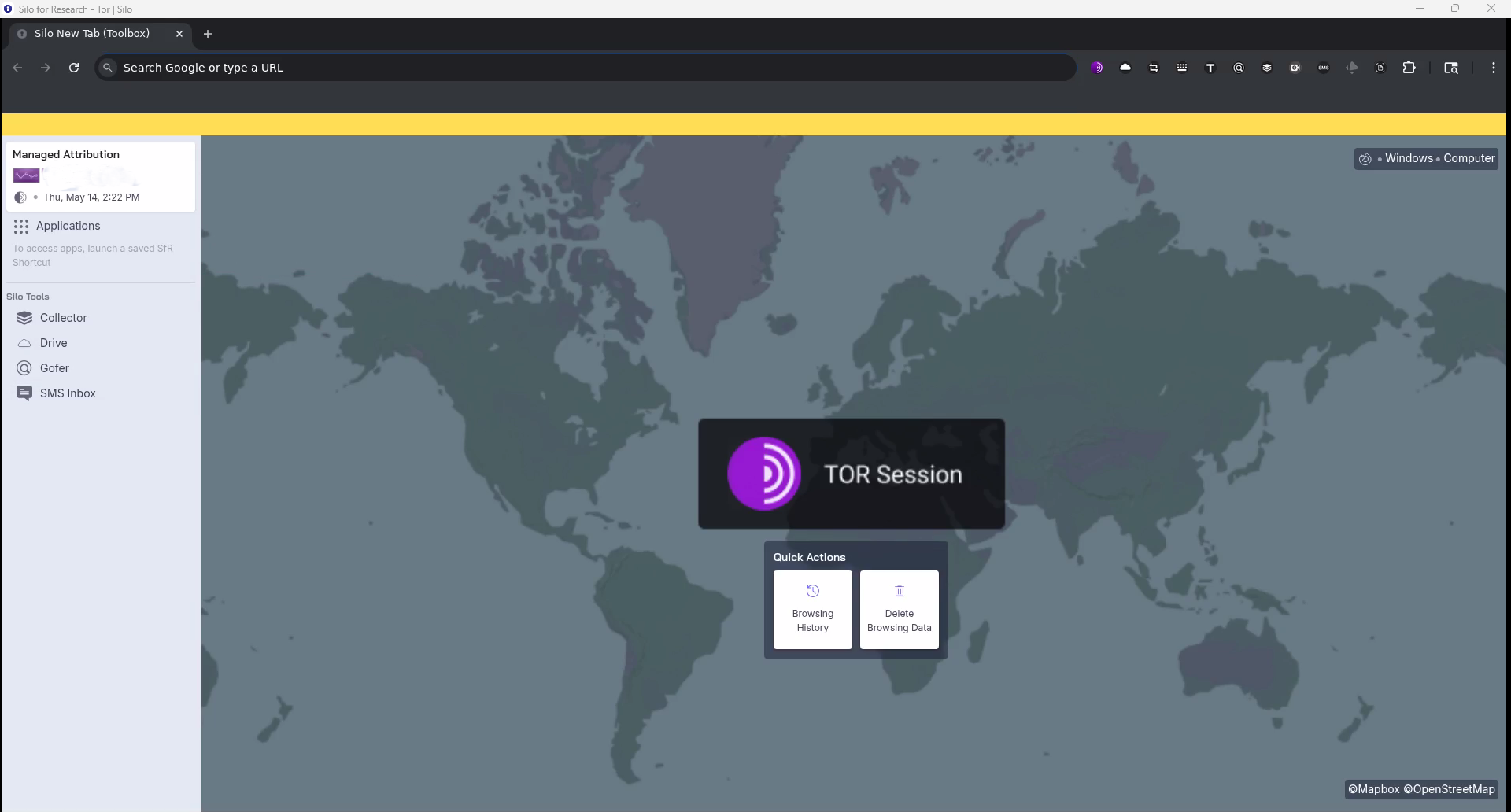
Step 1: Log into your Silo Workspace
Access is browser-based and cloud-delivered, meaning there is no need for dedicated hardware, OS configuration, or software installation.
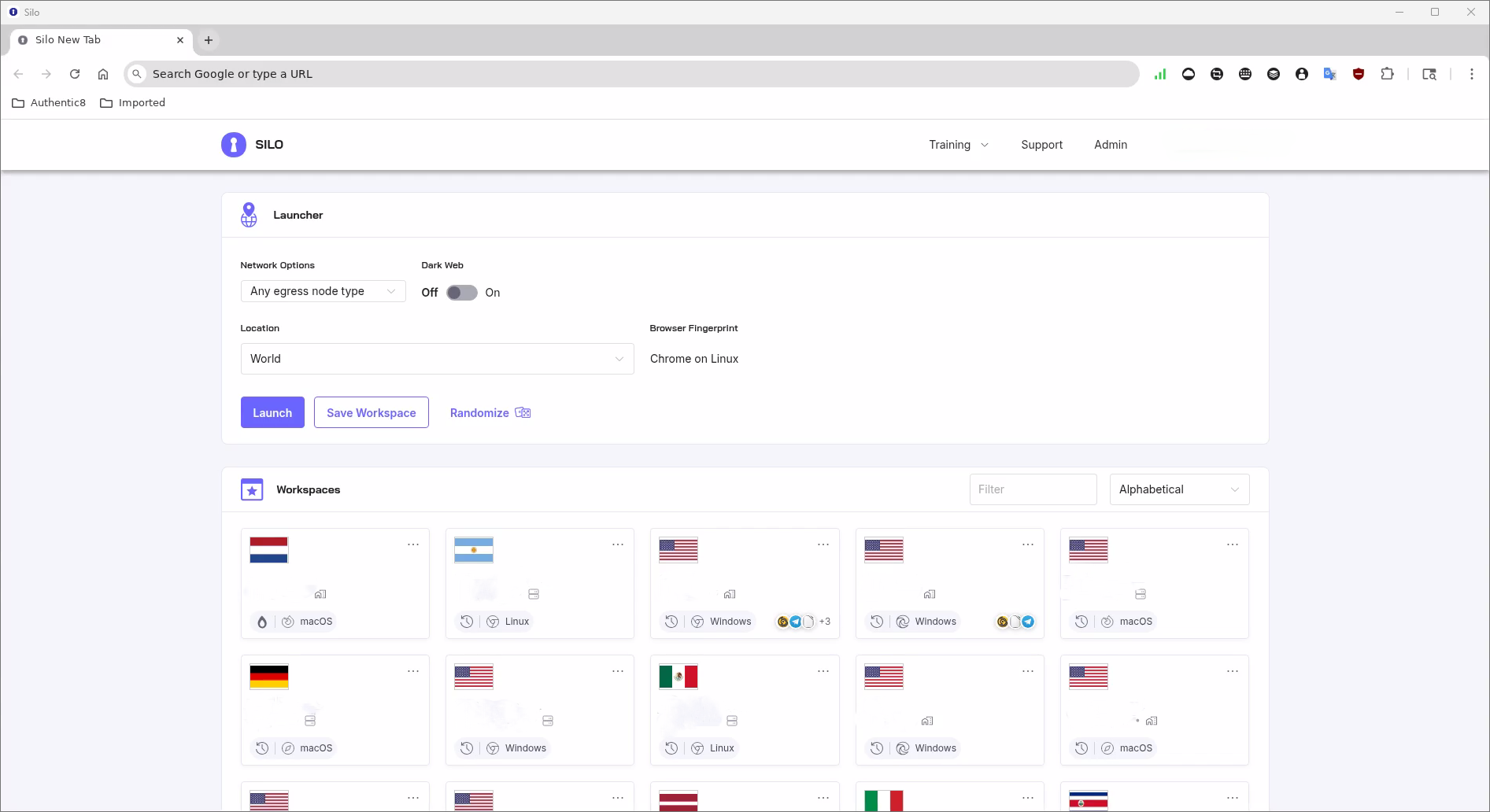
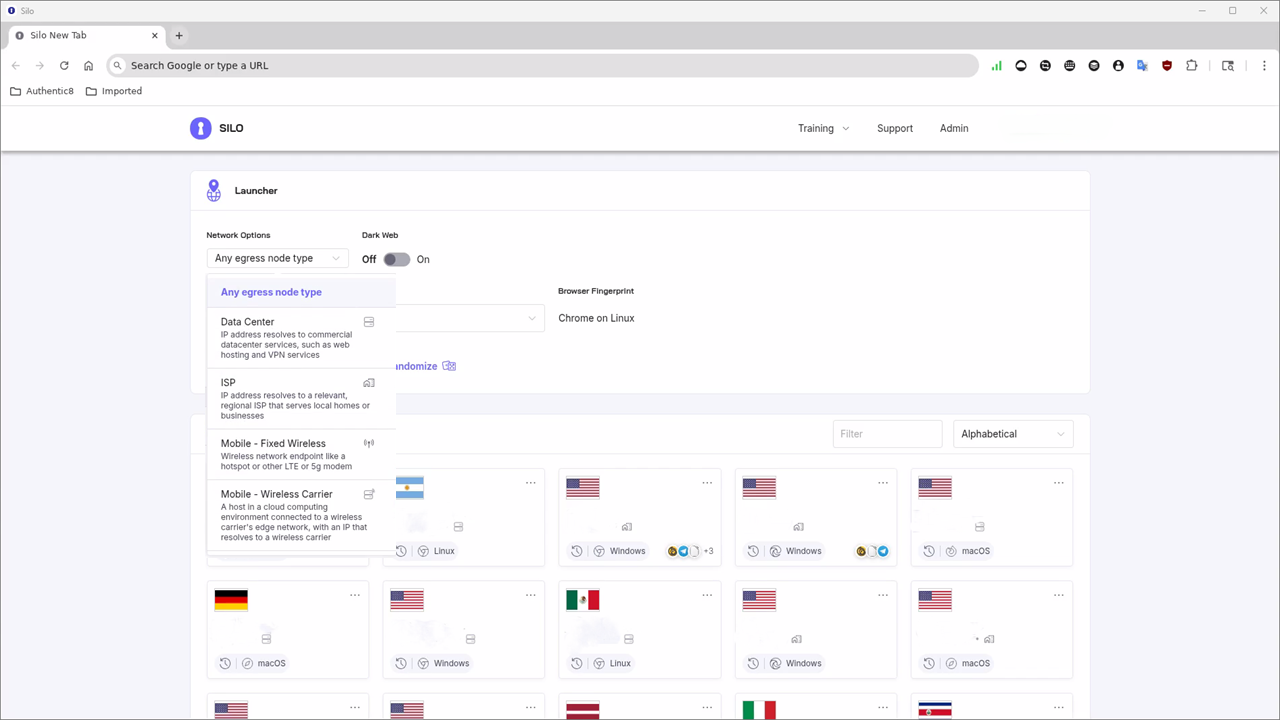
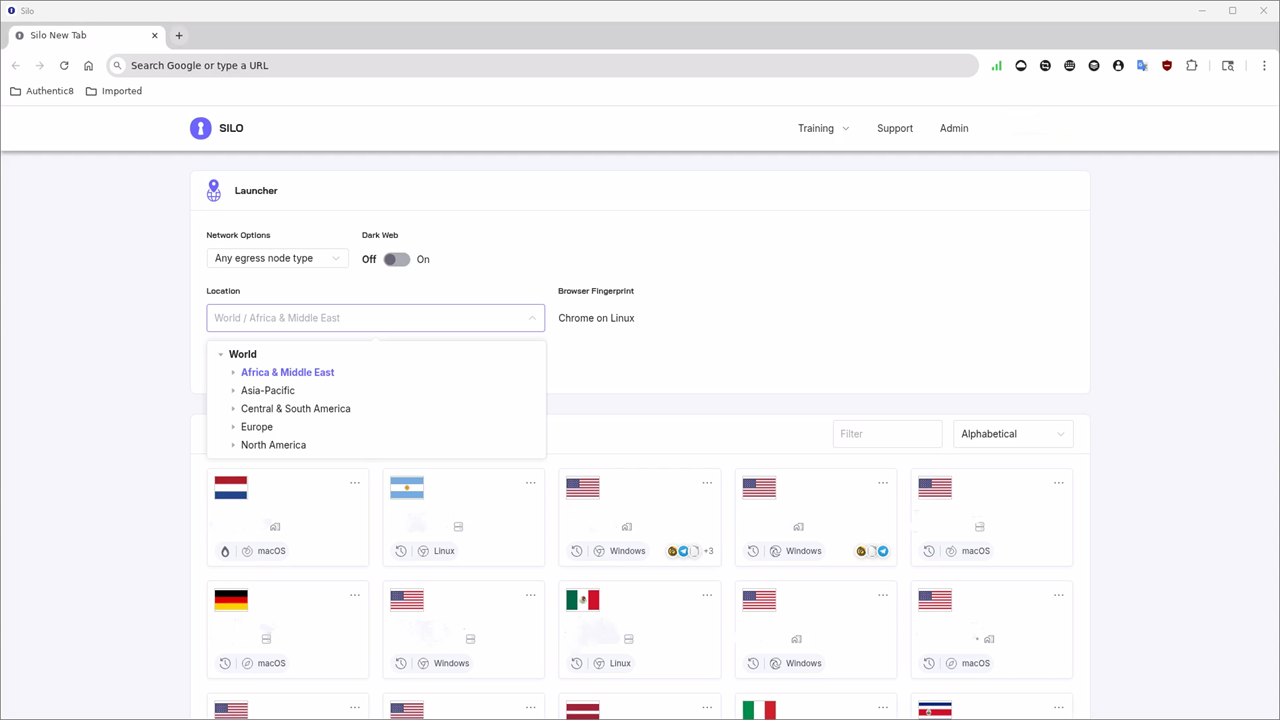
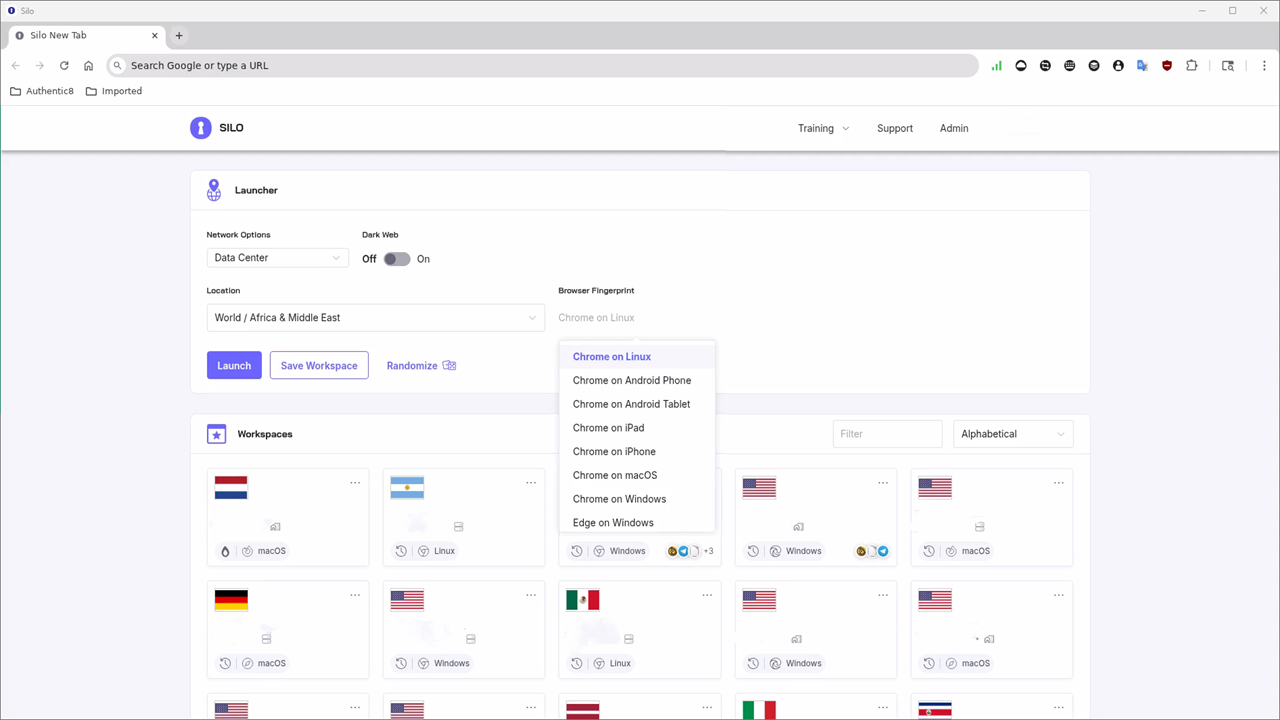
Step 2: Configure your managed attribution profile
Effortlessly customize your egress region, language, time zone, and browser fingerprint parameters, to instantly create hundreds of individual user experiences that can be disposable (one-time use) or persistent, depending on your needs. Silo's Managed Attribution (MA) Network routes traffic through more than 700 owned and operated endpoints across 32 countries, including Tor interconnects for dark web access, and can be configured to present across operating systems (Windows, Mac, Android, iOs, and Linux) and browsers (Edge, Firefox, Chrome, etc.). The investigator's real IP address, device, and organizational identity are never compromised.
Step 3: Launch a Dark Web workspace
Dark web access (including .onion sites) is integrated natively within Silo. No separate Tor browser installation is required. The session executes in an isolated cloud environment, meaning malicious content on target sites never reaches the investigator's device or network.
Step 4: Conduct the investigation
Browse, collect, and document using Silo's built-in tools. Screenshots, file captures, and session artifacts can be preserved to Silo Drive — Authentic8's encrypted, cloud-based storage — with automatic timestamping and chain-of-custody logging maintained throughout.
Step 5: Close the session
Choose to have your workspace persist for ongoing investigations or dispose of the session entirely. Either way, no residual data remains on the local device, and the full activity log is available for administrative review and legal defensibility.
Traditional dark web access methods vs. Silo Workspace
While a traditional approach can be effective, it demands significant time, technical expertise, and sustained operational discipline. Any mistakes, including connecting to the wrong network, an unverified download, a moment of persona inconsistency, risks exposure that defeats the entire effort. For organizations running high-volume or high-stakes investigations, maintaining that discipline at scale is incredibly difficult because even the best teams are still made up of humans…and humans make mistakes.
In contrast, Silo provides a managed, auditable platform that handles the hard parts automatically so the investigator can focus on the mission while operational security runs underneath their actions. This solution is not only simple and effective, but the benefits grow if the work is being conducted by a team – particularly a geographically dispersed team – where the risk of human error from a DIY solution would grow exponentially.
To see firsthand how tools like Silo can help you safely use the dark web in your investigation, experience Silo for yourself for 30 days or request a demo.
More from our dark web blog series:
- Leveraging the dark web in online investigations: Why you should utilize the dark web in your investigation, where to begin and how to protect yourself (and your company) along the way.
- 3 things to consider before you start your dark web investigation: When trying to determine if you should begin a dark web investigation, ask yourself these three questions concerning content, risk and precautions.
- Essential tools for improving surface and dark web research: Leveraging these easy-to-use dark web tools for surface as well as dark web investigations can help improve the quality and speed of your research.
- Best practices for creating a dark web access policy: Protect your company and employees by creating a dark web access policy to set protocols for investigations to mitigate security and legal challenges.
- 4 things you shouldn’t do on the dark web: Avoid a world of trouble by following these four simple recommendations of what not to do on the dark web during online investigations.
Dark web FAQs
Is the dark web illegal?
Accessing the dark web is generally legal, but many activities there are not. Investigators should avoid transacting, engaging, or downloading from illicit markets and use isolated, non-attributable browsing with audit logs. Consult organizational policy and legal counsel before any dark-web collection.
What’s the difference between deep web and dark web?
The deep web is content behind logins or paywalls and isn’t indexed, while the dark web is reachable only with special software like Tor and hosts hidden services (.onion). Deep-web access uses normal browsers; dark-web access requires specialized clients and stronger operational security.
How do I access the dark web safely?
Use a cloud-isolated, remote browser with non-attribution (managed identity, location, language), audit logging, and read-only file handling. Follow organizational rules of engagement and legal guidance. Avoid interacting with illicit markets or downloading untrusted files.
Can police track you on the dark web?
Yes. Dark-web users can be identified through operational mistakes, malware, de-anonymization, and service-level leaks. Investigators should assume attribution risk exists and rely on isolation, policy, and auditing rather than personal devices or consumer VPNs.
How much of the internet is the dark web?
The dark web is a very small portion of total internet traffic compared to surface and deep web content. Its significance stems from the types of data (forums, marketplaces, leaks), not its size. For investigations, safe access and governance matter more than volume.
What does .onion mean?
.onion is a pseudo-TLD used by hidden services on the Tor network. These sites aren’t indexed by traditional search engines and require Tor to access. Investigators should reach .onion resources via isolated, non-attributable browsers with logging and file controls.
What is non-attribution traffic?
Non-attribution traffic masks an analyst’s identity, location, device, and language to prevent linking research to real personas. Organizations implement it through managed browser isolation, identity controls, and audit logs, reducing risk during dark-web or high-risk surface-web collection.
What is SOCMINT?
SOCMINT (social media intelligence) is the collection and analysis of publicly available social-media data. For dark web investigations, SOCMINT often complements .onion research by correlating threat actor chatter, handles, and infrastructure across open, deep, and dark web sources.
Tags Dark web basics Dark web research


