New research indicates that eight out of ten CIOs and CISOs refrain from adopting an important security update or patch, due to concerns about the impact it might have on business operations.
More than half (52%) said they have done so on more than one occasion. What about in your organization?
The Global Resilience Gap study, commissioned by security software firm Tanium, polled 500 CIOs and CISOs in the United States, United Kingdom, Germany, France and Japan, in companies with 1,000+ employees. Its goal was to explore the challenges and trade-offs that IT operations and security leaders face in protecting their business from a growing number of cyber threats and disruptions.

Source: Tanium
The report identifies “[l]ack of visibility and control across networks” as the main cause behind such missed or delayed updates.
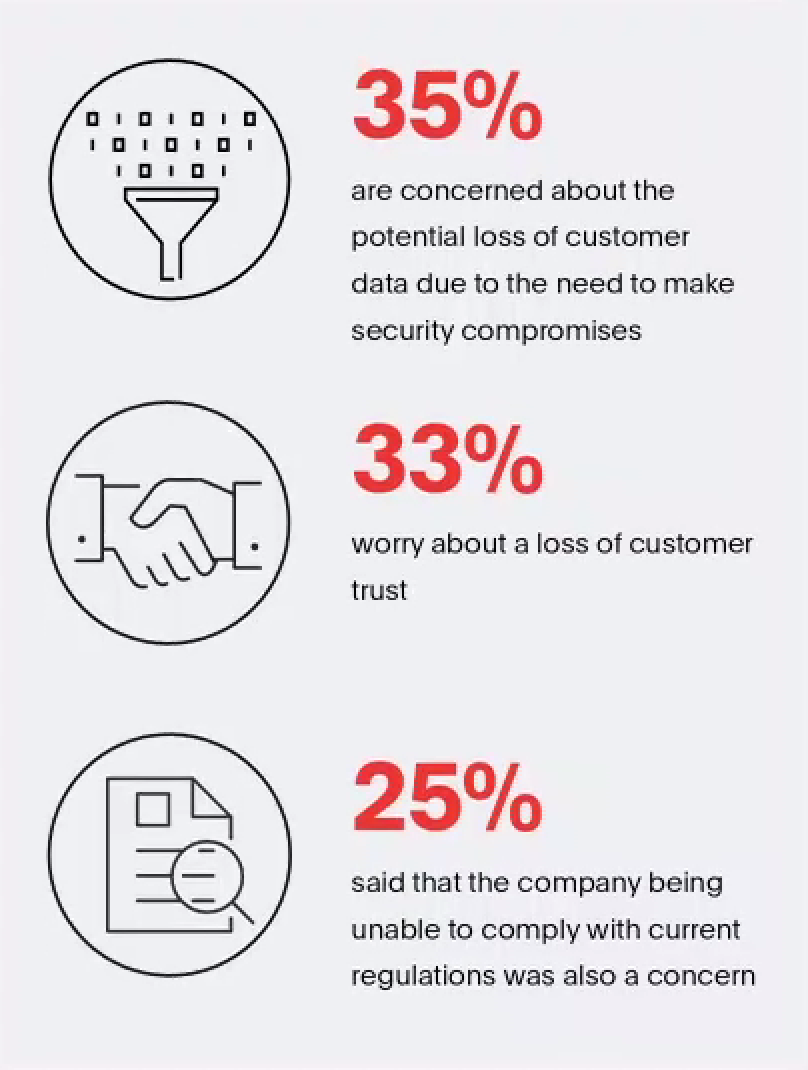
80% of respondents reported they found out that a critical update or patch they thought had been deployed had not actually updated all devices. This left their business exposed as a result. A quarter (25%) of respondents said that the company being unable to comply with current regulations was also a concern.
The vast majority of data breaches, security and compliance violations online can be traced back to the weak privacy, security and compliance posture of traditional browsers.
Not incidentally, such “free” browsers also require more updates and patches than any other application to maintain at least a basic resemblance of security, and IT has a hard time keeping up.
In most organizations, the primary tool for accessing the web has created a worrisome blind spot for IT. Updates and patches that happen too late or never, for instance due to a lack of qualified personnel, are increasing this risk.
What do a large-scale, automated ransomware attack and a rogue insider who is exfiltrating confidential data from the office via the web have in common?
Almost always, they both leverage the inherent vulnerabilities of regular “free” web browsers, which come with a steep hidden price tag. Locally installed browsers are notoriously difficult to maintain, secure, update, patch and monitor by IT and compliance managers.
Users - including, it appears, 81% of the CIOs and CISOs who responded to the survey - have succumbed to BFF - Browser Fiasco Fatigue. “Stop What You’re Doing and Update Google Chrome,” PCmag titled in March, echoing a warning issued by Google.
What are the chances? 19%?
When IT misses critical updates or patches, the consequences can be dire. The 2017 data breach at Equifax was traced back to a vulnerability for which a patch was available - it hadn’t been applied.
If you’re an 81-percenter, or simply want to avoid the trouble the survey results could spell for your business, you may be interested to learn that in 2019, organizations have an alternative.
Take NASA, for example. In 2016, the federal space agency reported that 426,000 critical patches had not been applied to more than 53,000 systems.
Fast forward to 2019: More than 100 federal agencies, including the Department of Defense, have either deployed, or are in the process of procuring, a secure cloud browser that doesn’t require them to install updates and patches anymore.
Source: Tanium
Is your IT team stretched too thin to keep up with the flood of browser update and confusing patch alerts? You don’t have to. Good riddance, BFF.
Enter Silo, the centrally managed, secure browser in the cloud delivered as-a-service by Authentic8, on our servers, outside our customers’ IT perimeter. With Silo, all web content is processed offsite in an isolated cloud container and transmitted back to the user through an encrypted connection as visual information. This makes it impossible for malware or tracking code to touch the endpoint or the corporate network.
For each web session, a new browser instance is built from scratch in the cloud and centrally configured to keep permissions and policies intact across departments, branch offices and subsidiaries, regardless of where the users are located or which device they use to access the web.
No resources left for updating to the latest and greatest (guaranteed secure!) version of a “free” browser? Are you tired of tying up the IT Department in Patch Tuesday parties?
Silo empowers your team to focus on other critical tasks that demand IT’s attention. This cloud browser enables your organization to...
reduce hard and soft costs through centralized browser management; the burden of managing and securing the browser shifts from IT to the provider;
centralize governance and oversight; a properly designed browser in the cloud like Silo provides management hooks that require only one-time implementation;
access the web anytime, anywhere without the loss of security or control, including from BYOD devices, which account for an ever-increasing share of (missed) updates and patches in many organizations.
No more missed updates and patches with this secure cloud browser. Silo also enables admins to handle identity and access management for authorized cloud-based apps centrally and to apply policies to allow or block key browser functionality, such as copy/paste or upload/download.
Another key advantage of the centralized cloud browser model pioneered by Authentic8: in tightly regulated industries, Silo allows for a unified view into all user activity during a web session, for centralized audit and compliance review.
Across a wide variety of sectors and industries, from financial institutions to law firms to law enforcement, many of the world’s most security-sensitive organizations now rely on Silo for secure, safe and productive access to the web.