Keeping up with changing technology trends and consumer preferences is no easy task. Companies need to keep a close eye on external factors that influence their business; sometimes this type of research needs to be done anonymously and in confidence.
Preserving confidentiality and anonymity is critical when conducting web-based corporate research. But the task of researching competitors and analyzing market trends often falls on business analysts — not security professionals — who may lack training in anonymous investigation techniques.

Corporate researchers typically aren’t trained in the operational security practices required to keep them safe and anonymous. Silo for Research is a simple and intuitive environment that ensures airtight security and anonymity, freeing analysts to conduct their research without risk.
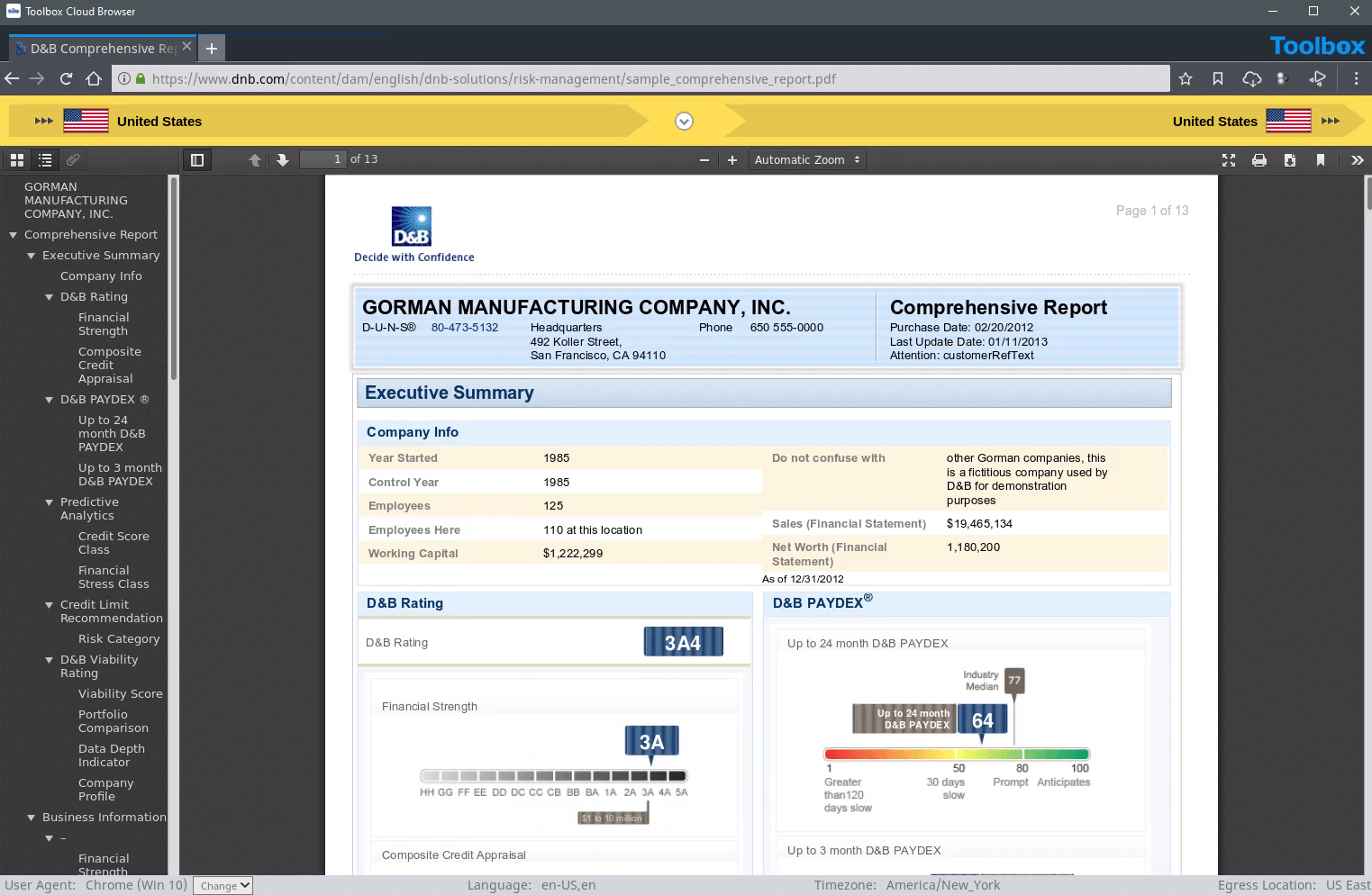
Corporate researchers collect fragmented data from disparate sources. That data may live on the web in different regions and networks. Silo for Research allows access and analysis of web-based resources regardless of location, language or network.
No web-native code ever reaches the analysts' desktop, no cookies are dropped and no exploits can transit the network. Silo for Research executes in a secure, cloud-based container, never exposing your IP addresses, devices identities or other resources directly to the internet.
Capturing disparate data may open the door to malicious content. Data captured in Silo for Research can be stored securely in the cloud, flattened into benign formats, or passed through multiple layers of antivirus processing to ensure the firm remains secure.
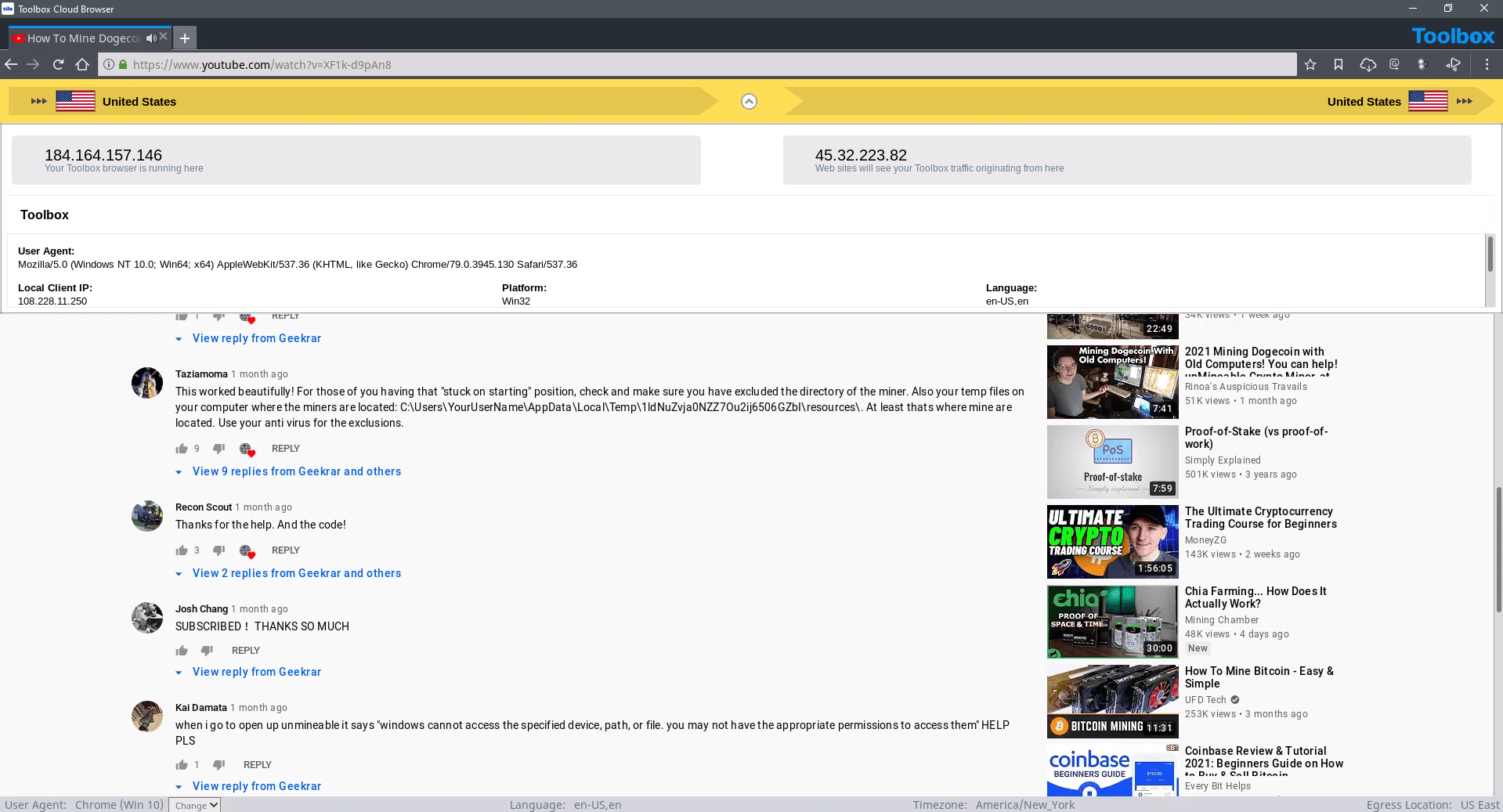
Data collections aren’t always passive; sometimes researchers may need to access forums or interact with parties outside their organization. Silo for Research enables full access to web-based forums and content hosting sites without exposing the environment or jeopardizing the investigation.
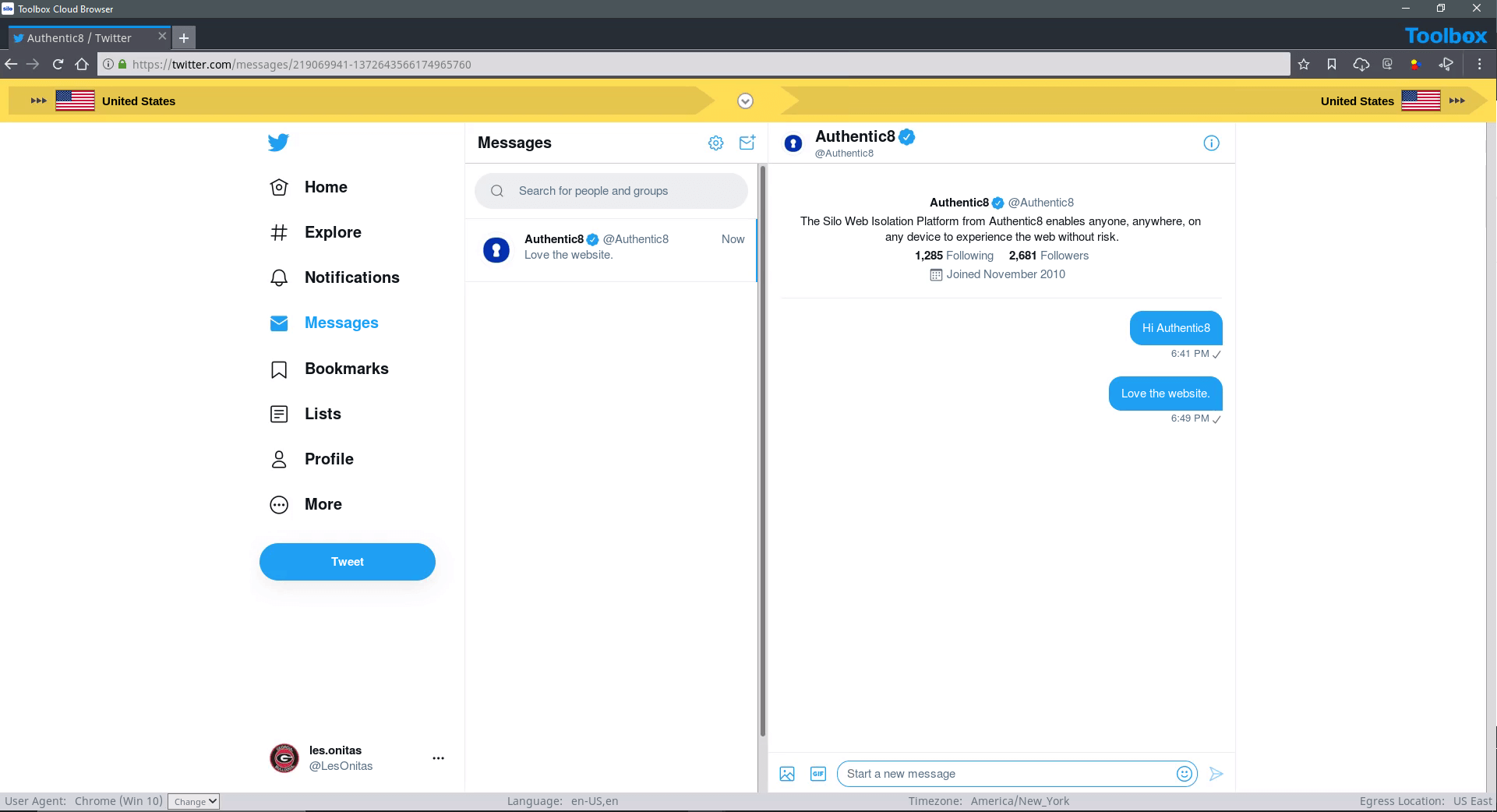




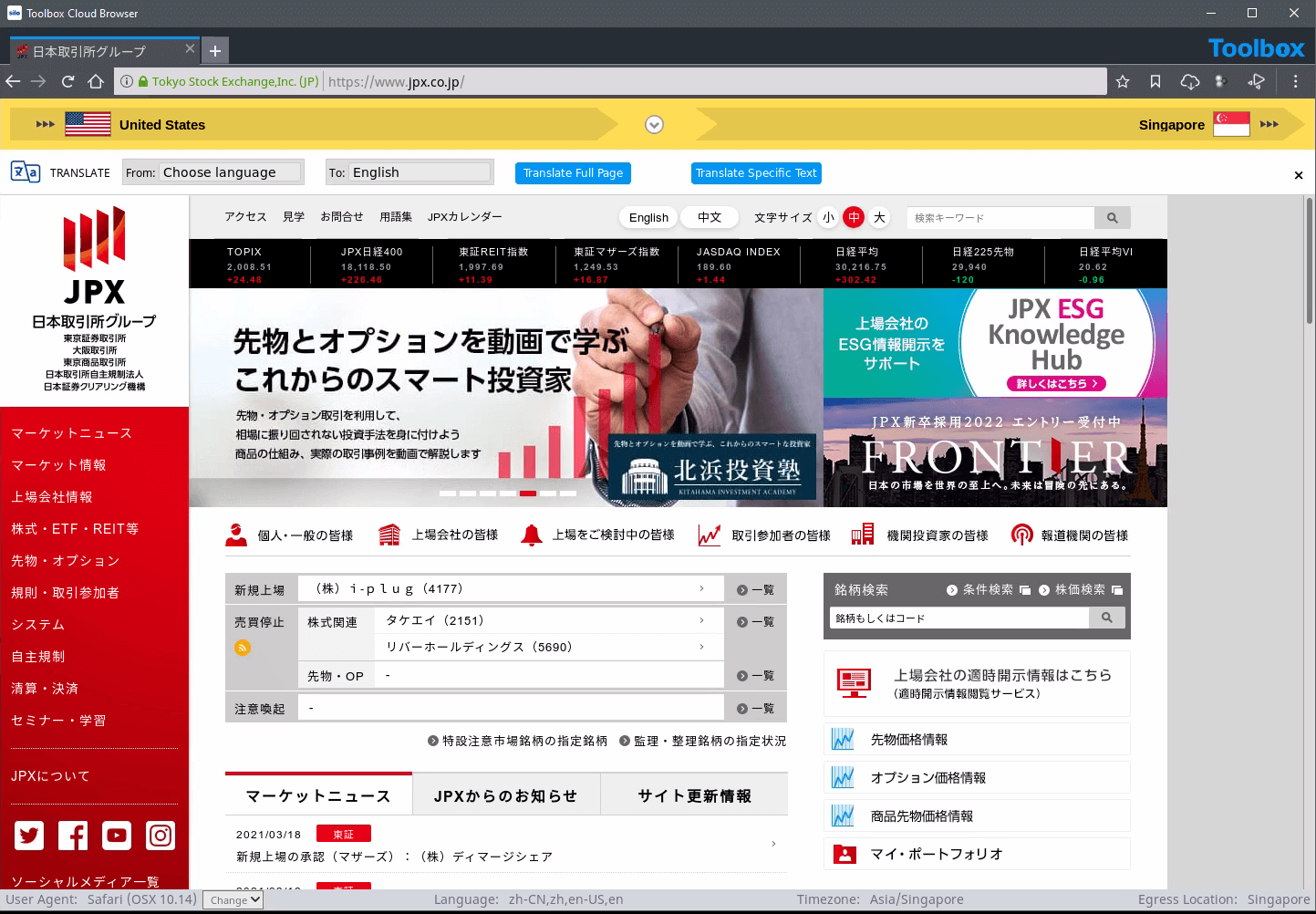
With Silo for Research's managed attribution functionality, you can completely customize how you appear to sites and people you interact with online. Manipulate a variety of your device details including language, time zone and keyboard settings, as well as the browser, OS and other elements. Appear to be browsing from any of Authentic8's dozens of global egress nodes, and show a local IP address that never refers back to you or your organization.
Yes, dark web access is seamlessly integrated within Silo for Research and its suite of analyst tools. You do not need a separate, standalone dark web browser. This integration provides investigators with full isolation from dark web cyberthreats (e.g., malware-laden sites, forums, marketplaces) and anonymity from counter-surveillance efforts utilized by malicious actors.
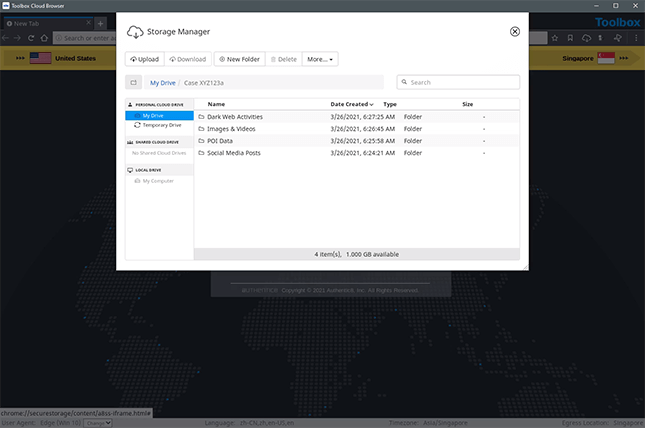
Yes, Silo for Research integrates with Authentic8 Secure Storage, an encrypted, audited and cloud-based storage repository for users and groups. Investigators may be required to capture and collect content as part of their process. And to maintain efficacy of potential evidence, a proper chain of control and evidentiary requirements must be met.
Collected data needs to be logged, attributed to an analyst and checked for validity. Chain of custody protections are critical to proper collection. When using Silo for Research collection tools — whether manual or automated — all aspects of the process are logged and available for post-facto review.
Yes, Silo for Research is a FedRAMP-authorized service. It has been assessed and approved as a cloud service offering (CSO) that meets the stringent security requirements to process, store and transmit federal government data.